ESET Research: Spy apps by the China-aligned GREF group pose as Signal and Telegram; attack users in Europe and the US
Created: 2023-09-01 06:27:27
- ESET Research has discovered trojanized Signal and Telegram apps for Android, named Signal Plus Messenger and FlyGram, on Google Play and Samsung Galaxy Store; both apps were later removed from Google Play.
- Signal Plus Messenger represents the first documented case of spying on a victim's Signal communications by secretly autolinking the compromised device to the attacker's Signal device.
- The malicious code found in these apps is attributed to the BadBazaar malware family, which has been used in the past by a China-aligned APT group called GREF.
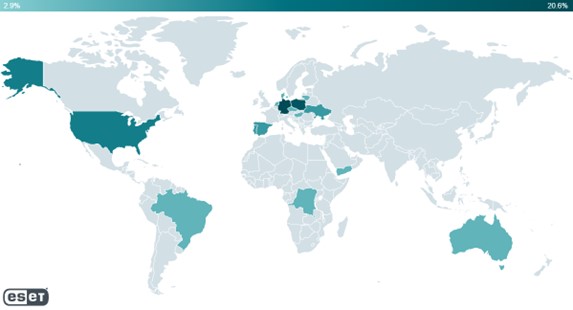
- Thousands of users downloaded the spy apps. ESET telemetry reported detections on Android devices in several EU countries, the United States, Ukraine, and other places worldwide.
- BadBazaar malware has previously been used to target Uyghurs and other Turkic ethnic minorities. FlyGram malware was also seen shared in an Uyghur Telegram group, which aligns with previous targeting by the BadBazaar malware family.
BRATISLAVA, KOŠICE — August 30, 2023 — ESET researchers have identified two active campaigns targeting Android users, where the threat actors behind the tools for Telegram and Signal are attributed to the China-aligned APT group GREF. Most likely active since July 2020 and since July 2022, respectively for each malicious app, the campaigns have distributed the Android BadBazaar espionage code through the Google Play store, Samsung Galaxy Store, and dedicated websites posing as legitimate encrypted chat applications — the malicious apps are FlyGram and Signal Plus Messenger. The threat actors achieved the functionalities in the fake Signal and Telegram apps by patching the open-source Signal and Telegram apps for Android with malicious code. Signal Plus Messenger is the first documented case of spying on a victim's Signal communications; thousands of users downloaded the spy apps. ESET telemetry reported detections on Android devices in several EU countries, the United States, Ukraine, and other places worldwide. Both apps were later removed from Google Play.
“Malicious code from the BadBazaar family was hidden in trojanized Signal and Telegram apps, which provide victims a working app experience but with espionage happening in the background,” says ESET researcher Lukáš Štefanko, who made the discovery. “BadBazaar’s main purpose is to exfiltrate device information, the contact list, call logs, and the list of installed apps, and to conduct espionage on Signal messages by secretly linking the victim’s Signal Plus Messenger app to the attacker’s device,” he adds.
ESET telemetry reports detections from Australia, Brazil, Denmark, the Democratic Republic of the Congo, Germany, Hong Kong, Hungary, Lithuania, the Netherlands, Poland, Portugal, Singapore, Spain, Ukraine, the United States, and Yemen. Furthermore, a link to FlyGram in the Google Play store was also shared in a Uyghur Telegram group. Apps by the BadBazaar malware family previously have been used against Uyghurs and other Turkic ethnic minorities outside of China.
As a Google App Defense Alliance partner, ESET identified the most recent version of the Signal Plus Messenger as malicious and promptly shared its findings with Google. Following our alert, the app was removed from the Store. Both apps were created by the same developer and share the same malicious features, and the app descriptions on both stores refer to the same developer website.
After initial app start, the user has to log into Signal Plus Messenger via legitimate Signal functionality, just like they would with the official Signal app for Android. Once logged in, Signal Plus Messenger starts to communicate with its command and control (C&C) server. Signal Plus Messenger can spy on Signal messages by misusing the “link device” feature. It does this by automatically connecting the compromised device to the attacker’s Signal device. This method of spying is unique: ESET researchers haven’t seen this functionality being misused before by other malware, and this is the only method by which the attacker can obtain the content of Signal messages. ESET Research has informed Signal’s developers about this loophole.
With regard to the fake Telegram app, FlyGram, the victim has to log in via their legitimate Telegram functionality, as required by the official Telegram app. Before the login is complete, FlyGram starts to communicate with the C&C server and BadBazaar gains the ability to exfiltrate sensitive information from the device. FlyGram can access Telegram backups if the user has enabled a specific feature added by the attackers; the feature was activated by at least 13,953 user accounts. The attacker’s proxy server may be able to log some metadata, but it cannot decrypt the actual data and messages exchanged within Telegram itself. Unlike the Signal Plus Messenger, FlyGram lacks the ability to link a Telegram account to the attacker or intercept the encrypted communications of its victims.
For more technical information about the latest campaigns by GREF, concerning BadBazaar and the trojanized espionage apps, check out the blogpost “BadBazaar espionage tool targets Android users via trojanized Signal and Telegram apps” on WeLiveSecurity. Make sure to follow ESET Research on Twitter for the latest news from ESET Research.
ESET telemetry for the trojanized apps.
About ESET
ESET develops software solutions that deliver instant, comprehensive protection against evolving computer security threats. ESET pioneered and continues to lead the industry in proactive threat detection. ESET NOD32 Antivirus, its flagship product, consistently achieves the highest accolades in all types of comparative testing and is the foundational product that builds out the ESET product line to include ESET Smart Security. ESET Smart Security is an integrated antivirus, antispyware, antispam and personal firewall solution that combines accuracy, speed and an extremely small system footprint to create the most effective security solution in the industry. Both products have an extremely efficient code base that eliminates the unnecessary large size found in some solutions. This means faster scanning that doesn’t slow down computers or networks. Sold in more than 160 countries, ESET has worldwide production headquarters in Bratislava, SK and worldwide distribution headquarters in San Diego, U.S. ESET also has offices in Bristol, U.K.; Buenos Aires, AR; Prague, CZ; and is globally represented by an extensive partner network. For more information, visit our local office at https://eset.version-2.sg.
About Version 2 Limited
Version 2 Limited is one of the most dynamic IT companies in Asia. The Company develops and distributes IT products for Internet and IP-based networks, including communication systems, Internet software, security, network, and media products. Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 Limited offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which includes Global 1000 enterprises, regional listed companies, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities. For more information, please visit https://www.version-2.com.sg/ or call (65) 6296-4268.

