ESET Smart Security utilizes the power of the cloud and multiple layers of detection to keep out threats and block
all potential attacks vectors protecting you at the highest level while you work, social network, play online games
or exchange data via removable media.
All-in-one Security Suite
ESET Smart Security 5 keeps your computer or laptop safe with intelligent multi-layered protection combining proven antivirus, antispyware, firewall, anti-rootkit and antispam capabilities.
Next Gen Security
The new generation of computer security boasts a large array of security features, usability enhancements and scanning technology improvements in defense of your your online life.
Bulking up Your Defenses
We have built a high-performing security solution against all internet threats, and to secure your personal data and sensitive information whether online or off. Take your computer security to a whole new level.
Key Features and Benefits
ESET Live Grid (Cloud-powered Repu![]() tation) NEW
tation) NEW
Delivers optimized real-time protection against Internet threats and social media exploits.
![]() Parental Control NEW
Parental Control NEW
Protects your family from potentially offensive web content by blocking various website categories.
Smart Detection![]()
Advanced heuristic detection technology flags even never-before-seen malware protecting you from unknown threats and neutralizing them before they can do any harm.
Intelligent Firewall ![]()
New and improved firewall module prevents unauthorized users from accessing your computer and taking advantage of your personal data.
Improved Antispam![]()
Tightly integrated into ESET Smart Security, the antispam module has undergone a thorough optimization for even higher level of filtering precision.
![]() Enhanced Media Control NEW
Enhanced Media Control NEW
Automatically scans all USB flash drives, memory cards and CDs/DVDs. Block removable media based on type of media, manufacturer, size and other attributes.
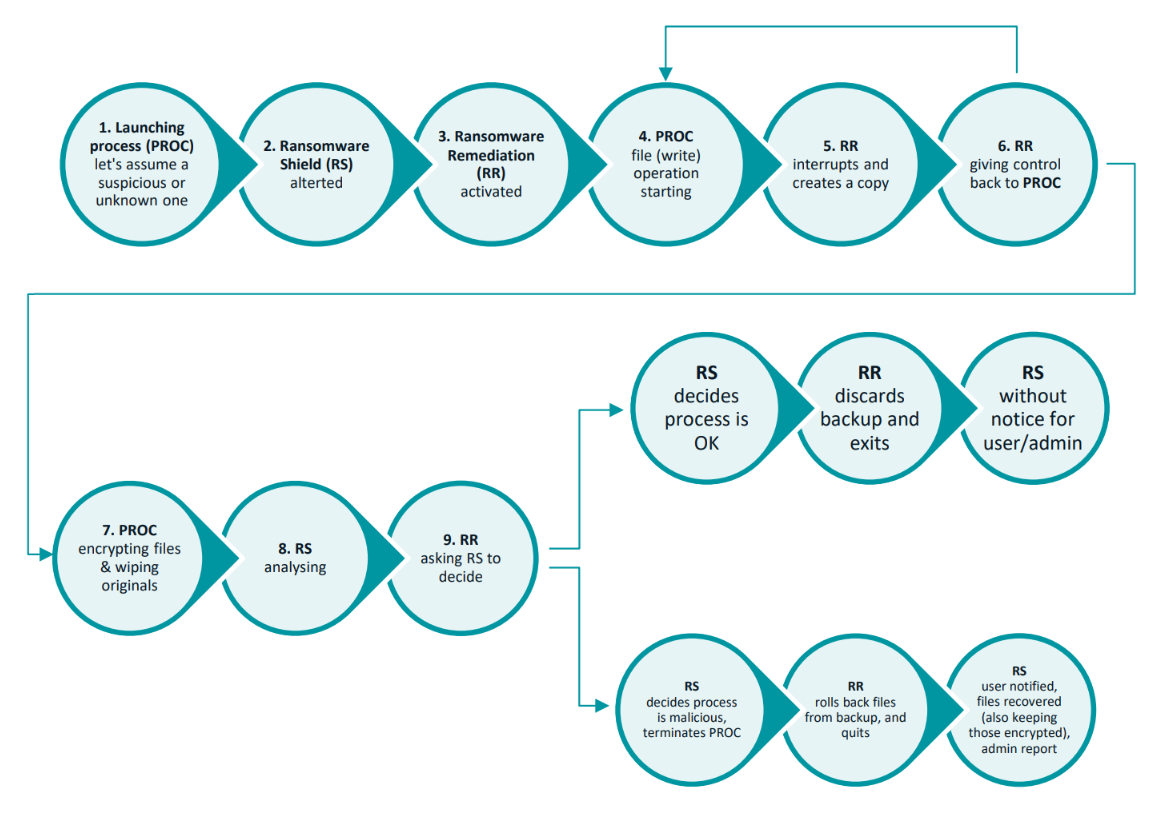
![]() Advanced HIPS Functionality NEW
Advanced HIPS Functionality NEW
This one is for real geeks – now you can customize the behavior of the system in greater detail: specify rules for the system registry, active processes and programs, and fine-tune your security posture.
Gamer Mode NEW![]()
Postpones all pop-up windows, updates or other system-intensive activities to conserve system resources for gaming or other full-screen activities.
Optimized Startup Procedure NEW![]()
No more waiting for signature database download to complete – ESET Smart Security 5 lets you start working immediately after booting, without compromising your security.
ESET Unilicense – Secure them All! 
ESET's unique Unilicense system allows you to extend protection to all operating systems running on a single machine – Windows, Mac OS or Linux – at no additional cost!
With Unilicense, multi-license holders can deploy ESET security solutions on operating systems of choice in a mix-and-match fashion to meet all their security needs.
Engineered around You: Just install and forget
User-centered Layout puts you in perfect control with the deshboard-like look of the "Tools" panel that is now even more intuitive and transparent. Also the most frequently used actions are available from all screens.
Find Your Own Security Posture with intuitive interface and fine-tuning options lets you find the best-fit security posture and keeps you abreast of vital security events and overall security status.
Light Footprint ensures a continual level of protection and smooth performance, while the energy-saving mode conserves resources even further - ideal for laptop users and gamers.
Awards
![]()
![]() AV-Comparatives – ESET has received the most "Advanced+" awards in proactive tests from AV-Comparatives of all Antivirus vendors.
AV-Comparatives – ESET has received the most "Advanced+" awards in proactive tests from AV-Comparatives of all Antivirus vendors.
Virus Bulletin – ESET NOD32 Antivirus has achieved the highest number of Virus Bulletin VB100 Awards, and never missed a single "In the Wild" virus, a testament to the consistent high-quality performance of ESET security across all platforms.
System Requirements
Processor Architecture
i386 (Intel® 80386), amd64 (x86-64)
Operating Systems
Microsoft Windows 2000
Microsoft Windows XP
Microsoft Windows Vista
Microsoft Windows 7
Microsoft Windows Home Server
Free Disk Space: 400 MB
Memory Consumption: 100 MB
Internet connection is required for product activation.